APPLICATIONS
HOT NEWS
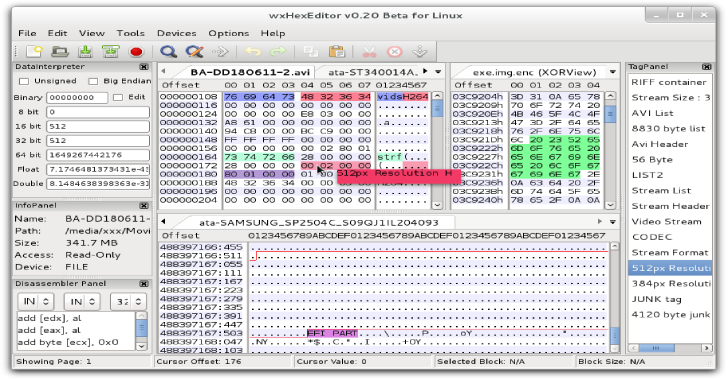
pwnSpoof : Generates realistic spoofed log files for common web servers...
pwnSpoof (from Punk Security) generates realistic spoofed log files for common web servers with customizable attack scenarios.
Every log bundle is unique and completely customisable, making...
© kalilinuxtutorials.com 2025