APPLICATIONS
HOT NEWS
SharpIncrease – Mastering Malware Obfuscation To Bypass Security Detection
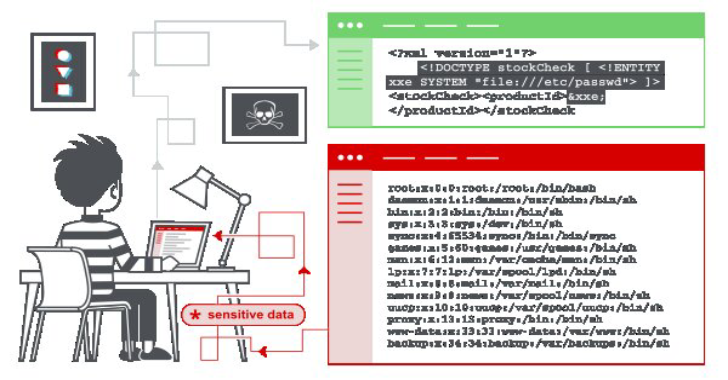
Adversaries may use binary padding to add junk data and change the on-disk representation of malware.
This can be done without affecting the functionality...
© kalilinuxtutorials.com 2025