APPLICATIONS
HOT NEWS
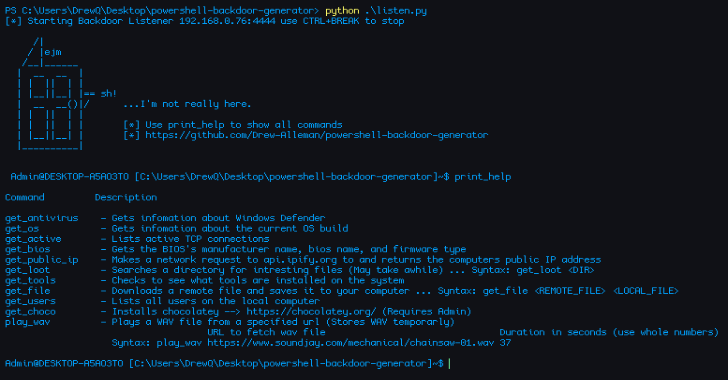
Powershell-Backdoor-Generator : To Create A Flipper Zero/ Hak5 USB Rubber Ducky...
Powershell-Backdoor-Generator is a reverse backdoor written in Powershell and obfuscated with Python. Allowing the backdoor to have a new signature after every build. With...
© kalilinuxtutorials.com 2025










.png)
.png)
.png)
.png)

.png)
.png)
.png)