APPLICATIONS
HOT NEWS
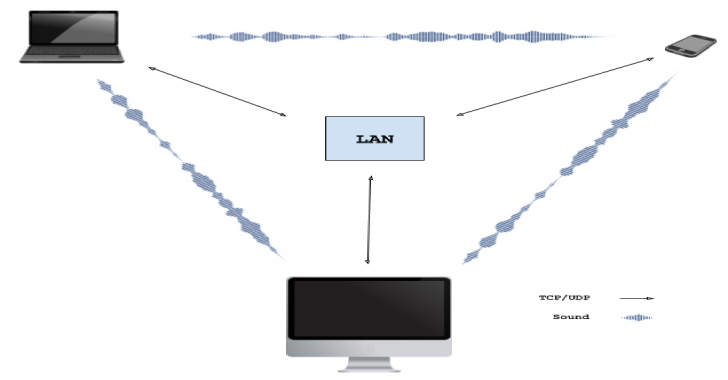
Wave-Share : Serverless, Peer-To-Peer, Local File Sharing Through Sound
A proof-of-concept for WebRTC signaling using sound. Works with all devices that have microphone + speakers. Runs in the browser.
Nearby devices negotiate the WebRTC...
© kalilinuxtutorials.com 2025