APPLICATIONS
HOT NEWS
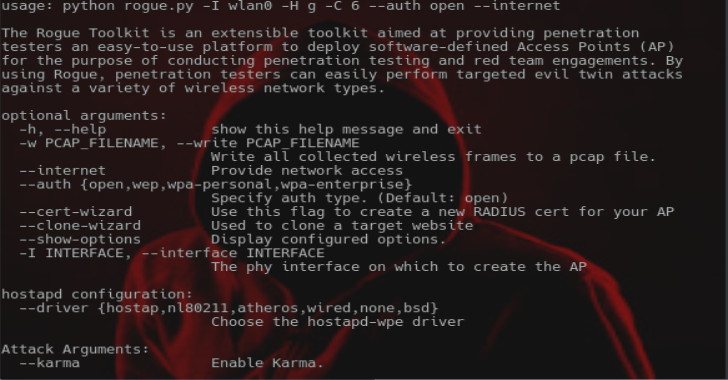
Rogue : An Extensible Toolkit Providing Penetration Testers An Easy-To-Use Platform
The Rogue Toolkit is an extensible toolkit aimed at providing penetration testers an easy-to-use platform to deploy software-defined Access Points (AP) for the purpose...
© kalilinuxtutorials.com 2025