APPLICATIONS
HOT NEWS
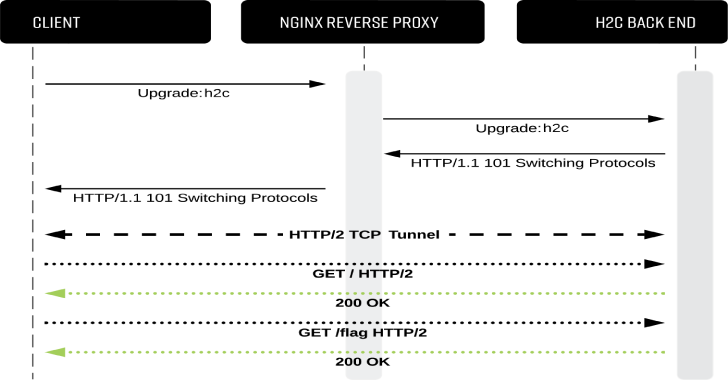
h2cSmuggler : HTTP Request Smuggling Over HTTP/2 Cleartext (H2C)
h2cSmuggler smuggles HTTP traffic past insecure edge-server proxy_pass configurations by establishing HTTP/2 cleartext (h2c) communications with h2c-compatible back-end servers, allowing a bypass of proxy...
© kalilinuxtutorials.com 2025